Blog
Announcing Contour v1.12.0
Feb 2, 2021
Contour continues to add new features to help you better manage ingress operations in a cluster.
Our latest feature release, Contour 1.12.0, adds support for local rate limiting on HTTPProxy virtual hosts and routes, dynamic request headers, and header hash load balancing.
Local Rate Limiting
Rate limiting is a means of protecting backend services against unwanted traffic. This can be useful for a variety of different scenarios:
- Protecting against denial-of-service (DoS) attacks by malicious actors
- Protecting against DoS incidents due to bugs in client applications/services
- Enforcing usage quotas for different classes of clients, e.g. free vs. paid tiers
- Controlling resource consumption/cost
Envoy supports two different types of rate limiting: local and global. In local rate limiting, a rate limit is applied to traffic by each individual Envoy process/pod, without sharing information across multiple instances of Envoy. In global rate limiting, all Envoy instances communicate with an external Rate Limit Service (RLS) via gRPC to make rate limit decisions.
Contour 1.12.0 adds support for Envoy’s local rate limiting.
This enables Contour users to protect their backend services by defining simple limits for how much traffic each Envoy process/pod should proxy to them.
Local rate limits can be defined for an entire virtual host, or for individual routes.
Here’s an example of an HTTPProxy that allows 100 requests per second from each Envoy pod to reach a backend service:
apiVersion: projectcontour.io/v1
kind: HTTPProxy
metadata:
name: ratelimited-route
spec:
virtualhost:
fqdn: ratelimit.projectcontour.io
routes:
- conditions:
- prefix: /ratelimited-service
services:
- name: s1
port: 80
rateLimitPolicy:
local:
requests: 100
unit: second
Requests above the 100-per-second limit will receive a 429 (Too Many Requests) response by default.
The response code can also be customized.
For more information, see:
- the Contour Rate Limiting documentation
- the HTTPProxy API reference
- Envoy’s HTTP local rate limit filter documentation
For users with more advanced rate-limiting needs, Contour will also be adding global rate limiting support in an upcoming release.
Dynamic Request Headers
Contour 1.12 also adds support for including dynamic values in configured request and response headers. Almost all variables supported by Envoy are allowed. This feature can be used to set headers containing information such as the host name of where the Envoy pod is running, the TLS version, etc.
For more information, including a full list of supported variables, see the Contour documentation.
A big thanks to @erwbgy for designing and implementing this feature!
Header Hash Load Balancing
Contour 1.12 now supports the RequestHash load balancing strategy, which enables load balancing based on request headers.
An upstream Endpoint is selected based on the hash of an HTTP request header.
Requests that contain a consistent value in a request header will be routed to the same upstream Endpoint.
For more information, including an example HTTPProxy definition, see the
Contour documentation.
Community Thanks!
We’re immensely grateful for all the community contributions that help make Contour even better! For version 1.12, special thanks go out to the following contributors:
Related Content
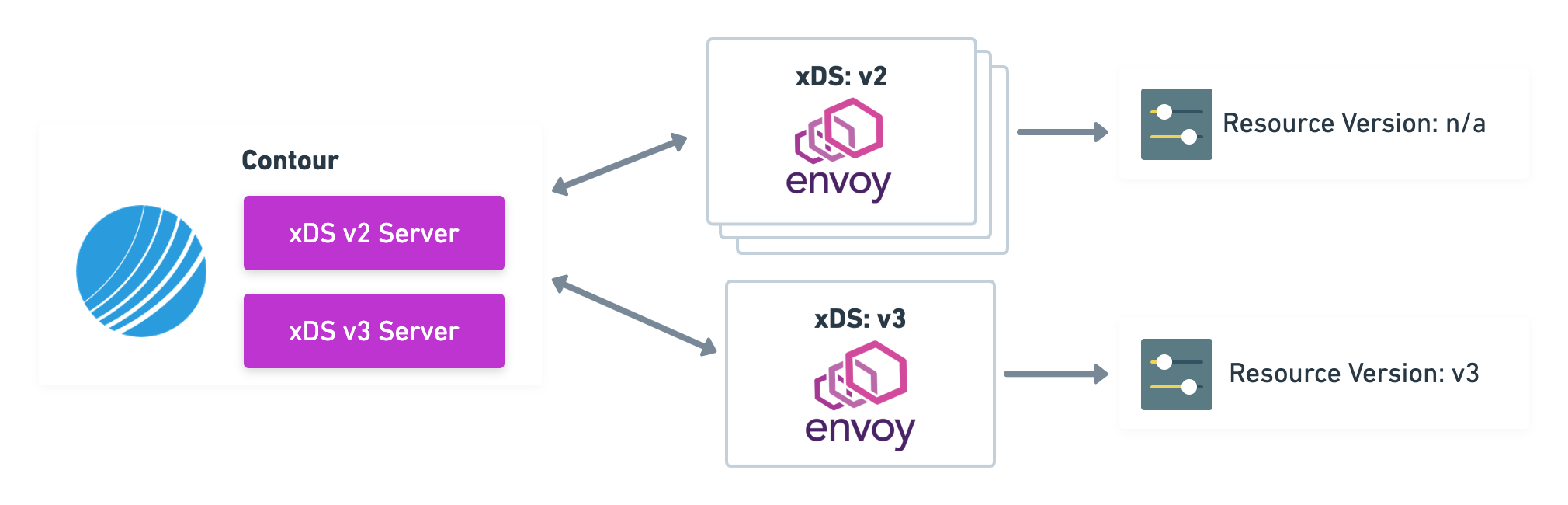
Announcing Contour v1.10.0
This blog post covers xDS Resource Server conversion from v2 to v3 in Contour v1.10.0.
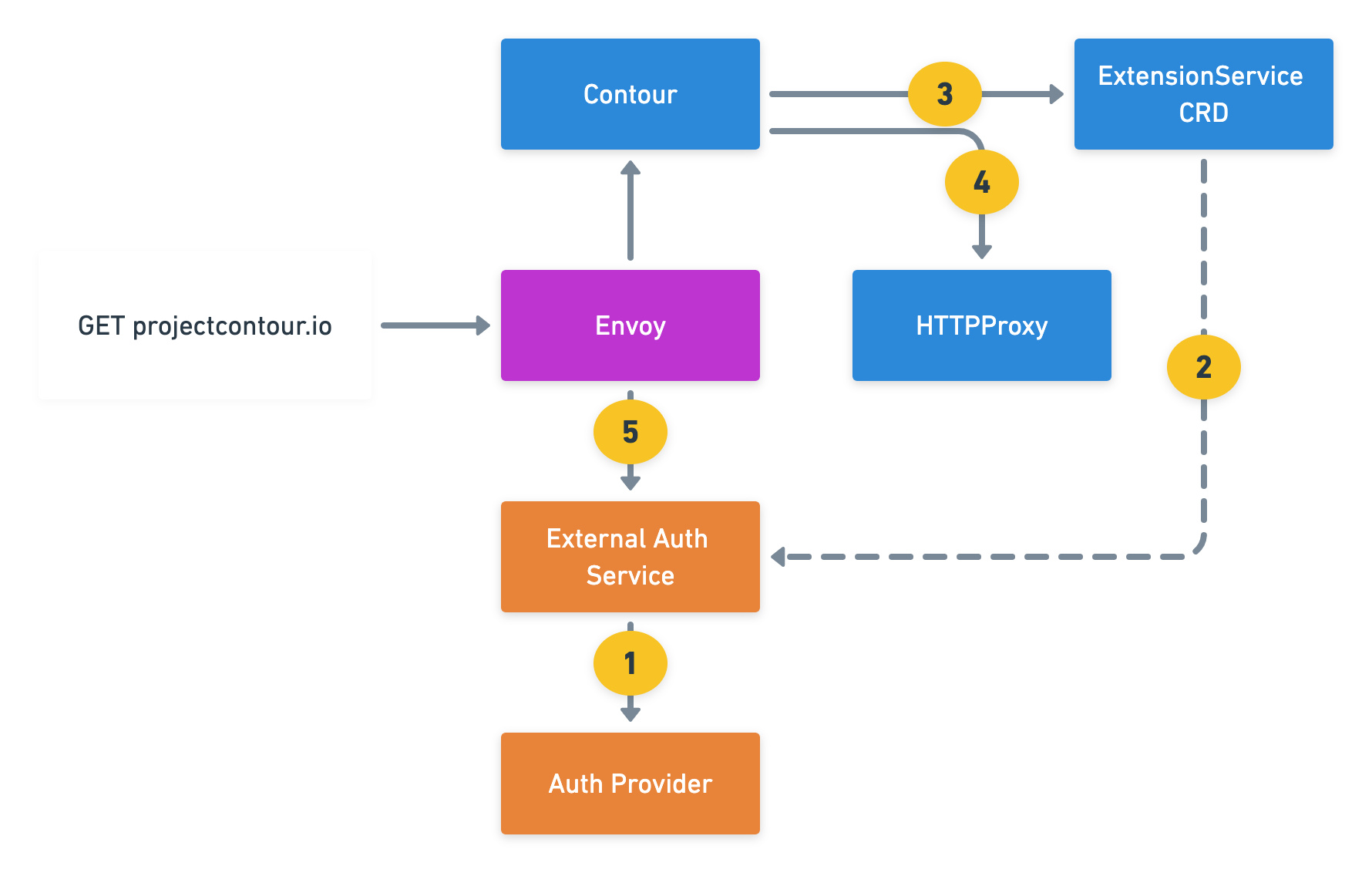
Announcing Contour v1.9.0
This blog post covers External Authorization and Cross-Origin Resource Sharing (CORS) Support in Contour v1.9.0.

Contour’s landscape, July 2020
Contour is now part of the CNCF, and we're taking the opportunity to reevaluate our product philosophy.
 Twitter
Twitter Slack
Slack RSS
RSS GitHub
GitHub